Technical Advisory: TeamPCP Supply Chain Campaign
A threat actor compromised the Trivy vulnerability scanner and used stolen CI/CD secrets to cascade into Checkmarx, LiteLLM, and 50+ npm packages. Includes active IOCs and guidance for agentic AI teams.

Disclosed: March 19, 2026
Severity: Critical
Package/Component: trivy-action • trivy • setup-trivy • litellm
Advisories: Aqua Security – Official Trivy Supply Chain Advisory • Endor Labs – TeamPCP Isn’t Done
Executive Summary
What Happened: A threat actor identified as TeamPCP compromised Aqua Security’s Trivy vulnerability scanner on March 19, 2026, injecting credential-harvesting malware into official GitHub Actions and release binaries. Over the following five days, the campaign expanded to Checkmarx, LiteLLM (PyPI), and more than 50 npm packages, leveraging credentials stolen from the initial compromise to move laterally across multiple ecosystems.
Why It Matters:
- Supply Chain Integrity: Security tooling – the tools organizations rely on to catch supply chain risk – became the attack vector itself, undermining a foundational layer of CI/CD trust.
- Credential and Infrastructure Exposure: Secrets harvested from pipeline execution provide direct access to cloud infrastructure, Kubernetes clusters, and internal systems, with no user interaction required.
- Agentic AI Pipeline Risk: Agentic systems that dynamically invoke npm and Python packages inherit the same exposure. Compromised packages can exfiltrate credentials the agent operates with, including credentials that flow through the environment without the agent directly handling them.
- Cascading Blast Radius: Credentials stolen from one project enabled compromise of at least two additional downstream projects within five days, demonstrating the compounding effect of CI/CD secret reuse across teams.
High-Level Risks:
- Credential theft (GitHub PATs, cloud provider tokens, Kubernetes secrets, SSH keys)
- Lateral movement into connected projects and infrastructure
- Persistent backdoor installation via systemd services and privileged Kubernetes pods
- Data exfiltration via decentralized C2 infrastructure resistant to traditional domain blocking
Immediate Actions:
- Pin
trivy-actionto v0.35.0 andtrivyto v0.69.3 using commit SHAs - Rotate all secrets accessible to pipeline runners that executed between March 19 and March 24, 2026
- Audit Kubernetes clusters for unauthorized privileged pods and new systemd services
- Block
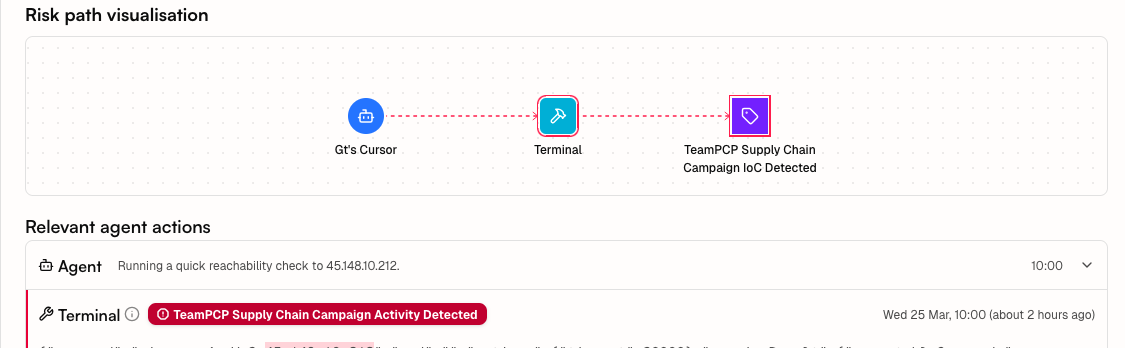
scan.aquasecurtiy[.]org(45.148.10.212) at the network perimeter
Overview
On March 19, 2026, TeamPCP force-pushed malicious commits to 76 of 77 version tags of the trivy-action GitHub Action and published backdoored Trivy scanner binaries to GitHub Releases, Docker Hub, GHCR, and Amazon ECR. The initial access vector traces to a CI/CD misconfiguration exploited in late February 2026; credential rotation on March 1 was incomplete, leaving residual access that enabled the March 19 attack. CanisterWorm, a self-spreading npm worm using stolen publish tokens, was first detected on March 20, ultimately infecting 64–66 packages (135–141 malicious artifacts). The campaign expanded on March 24 to Checkmarx and LiteLLM using credentials harvested from Trivy pipeline users.
Risk Analysis
This threat is particularly concerning in the context of agentic AI systems due to:
- Security tooling as attack surface: Trivy is embedded in CI/CD pipelines specifically to detect supply chain risk. Compromising it converts a defense mechanism into a credential harvester operating with pipeline-level trust.
- Credential reuse enabling cascading compromise: Secrets harvested from Trivy users unlocked downstream access to Checkmarx and LiteLLM within the same campaign window, illustrating how a single CI/CD compromise can propagate across an organization’s toolchain.
- Decentralized C2 infrastructure: The campaign uses an Internet Computer Protocol (ICP) canister as a fallback command-and-control channel, making it resistant to traditional domain-level blocking and harder to fully remediate without addressing the worm propagation mechanism.
Technical Details
- Initial access via CI/CD misconfiguration (late February 2026):
- A bot named
hackerbot-clawexploited a misconfiguredpull_request_targetworkflow in Trivy’s GitHub repository on February 28, extracting a privileged PAT (ORG_REPO_TOKEN) with write access to all 33+ Aqua Security repositories - The extracted token was used to backdoor the Trivy VS Code extension on Open VSX (versions 1.8.12 and 1.8.13), injecting hidden natural-language prompts directing locally installed AI coding assistants (Claude, Copilot, Gemini, Codex, Kiro) to collect system information and authentication tokens and exfiltrate them via the victim’s GitHub CLI
- Aqua Security disclosed the intrusion on March 1 and rotated credentials, but the rotation was incomplete; the attacker retained access through a still-valid service account credential
- Residual access enabled the March 19 attack
- A bot named
- Credential harvesting from pipeline memory (March 19):
- Malicious code injected into
trivy-actionand the Trivy scanner binary harvested secrets from Runner.Worker process memory during pipeline execution - Targets included GitHub PATs, cloud provider tokens (AWS, GCP, Azure), Kubernetes secrets, SSH keys,
.envfiles, and crypto wallet credentials - Stolen tokens were exfiltrated to
scan.aquasecurtiy[.]org(45.148.10.212)
- Malicious code injected into
- Lateral expansion using stolen credentials (March 24):
- Credentials harvested from Trivy pipeline users enabled compromise of Checkmarx KICS and AST GitHub Actions
- LiteLLM versions 1.82.7 and 1.82.8 were backdoored on PyPI with the same infostealer payload plus a Kubernetes lateral movement component
- v1.82.8 additionally abused Python’s
.pthfile mechanism (litellm_init.pth), executing a double base64-encoded payload on any Python invocation regardless of whether LiteLLM was explicitly imported — the trigger scope extends beyond LiteLLM processes to any Python process on the host - The Kubernetes component deployed privileged pods to all cluster nodes and installed persistent systemd backdoors polling for additional payloads
- Worm deployment across the npm ecosystem (first detected March 20):
- CanisterWorm infected 64–66 npm packages (135–141 malicious artifacts) across multiple scopes (
@EmilGroup,@opengov,@teale.io,@airtm,@pypestream) using stolen publish tokens - Infection runs via a
postinstallhook that drops a Python backdoor and registers it as a persistent user-level systemd service (pgmon.service) - The backdoor polls ICP canister
tdtqy-oyaaa-aaaae-af2dq-caievery 50 minutes for a payload URL; the canister cannot be neutralised through conventional domain blocking - Self-propagation uses extracted npm tokens to increment patch versions and publish malicious updates to every package the compromised account maintains
- CanisterWorm infected 64–66 npm packages (135–141 malicious artifacts) across multiple scopes (
- Kubernetes wiper via ICP canister (identified March 22):
- The same ICP canister served a second payload targeting Kubernetes environments: a controller script that fingerprints locale (
/etc/timezone,timedatectl,LANG=fa_IR) to determine whether to wipe or persist - On Iranian-locale Kubernetes clusters: deployed DaemonSet
host-provisioner-iraninkube-systemwith a privileged Alpine container (kamikaze) that deleted host filesystem contents via mounted/mnt/hostand forced a reboot, effectively bricking each node - On non-Iranian Kubernetes clusters: deployed DaemonSet
host-provisioner-std, a persistent backdoor polling the same ICP canister for additional binaries - A third variant added SSH lateral movement: parsing auth logs for successful login pairs, stealing keys from
~/.ssh/, and spreading to/24subnet hosts and exposed Docker APIs on port 2375 - Indicators: DaemonSets
host-provisioner-iranorhost-provisioner-stdinkube-system; systemd services namedpgmon,internal-monitor, orpgmonitor; files at~/.config/sysmon/sysmon.pyor/var/lib/pgmon/pgmon.py
- The same ICP canister served a second payload targeting Kubernetes environments: a controller script that fingerprints locale (
Impact
Systems affected by this threat may experience:
- Exfiltration of CI/CD secrets including cloud provider credentials, GitHub PATs, and Kubernetes tokens accessible to pipeline runners
- Unauthorized access to cloud infrastructure and Kubernetes clusters via harvested credentials
- Persistent backdoor presence via systemd services on Kubernetes nodes
- Lateral movement into projects and pipelines sharing secrets with affected runners
- Self-spreading npm package compromise in environments where affected scopes are used
- Continued exposure while CanisterWorm propagation via the ICP canister C2 remains active
Affected Versions
The following versions are known to be affected:
| Component | Compromised Versions | Last Known Clean Version |
|---|---|---|
| Trivy scanner | v0.69.4, v0.69.5, v0.69.6 | v0.69.3 |
| trivy-action | 76 of 77 version tags | v0.35.0 |
| setup-trivy | All versions prior to fix | v0.2.6 |
| LiteLLM (PyPI) | v1.82.7, v1.82.8 | v1.82.6 |
| Checkmarx KICS | Affected via Actions | Verify with Checkmarx advisory |
| npm packages – CanisterWorm (64–66 packages, 135–141 malicious artifacts, partial list) | ||
| @emilgroup/discount-sdk | 1.5.1 | — |
| @emilgroup/document-uploader | 0.0.10 | — |
| @emilgroup/docxtemplater-util | 1.1.2 | — |
| @emilgroup/numbergenerator-sdk-node | 1.3.1 | — |
| @emilgroup/partner-portal-sdk | 1.1.1 | — |
| @emilgroup/setting-sdk | 0.2.1 | — |
| @emilgroup/task-sdk | 1.0.2 | — |
| @emilgroup/task-sdk-node | 1.0.2 | — |
| @teale.io/eslint-config | 1.8.11, 1.8.12 | — |
| @opengov/form-renderer | See GMS-2026-49 | — |
Trivy malicious versions (v0.69.4 – v0.69.6) have been removed from Docker Hub. The last clean Docker Hub image is v0.69.3.
Immediate Mitigation Steps
- Update and pin affected components:
# Pin trivy-action to safe version by commit SHA in your workflow
# uses: aquasecurity/trivy-action@<commit-sha-for-v0.35.0>
# Update Trivy scanner binary
# Pull v0.69.3 explicitly – do not use v0.69.4, v0.69.5, or v0.69.6
docker pull aquasec/trivy:0.69.3
- Rotate all secrets exposed during the March 19 – 24 window:
- Rotate GitHub Personal Access Tokens accessible to affected runners
- Rotate AWS, GCP, and Azure credentials used in affected pipelines
- Rotate Kubernetes service account tokens and kubeconfig credentials
- Treat all runners that executed Trivy between March 19 and March 24 as compromised
- Audit for active compromise indicators:
- Check GitHub organization for repositories with the
tpcp-docs-prefix (indicator of successful exfiltration) - Audit Kubernetes nodes for new systemd services and unauthorized privileged pods
- Review CloudTrail and cloud audit logs for unexpected API calls during the exposure window
- Check for outbound connections to
scan.aquasecurtiy[.]orgor the ICP canister identifier from CI/CD runners or Python processes
- Check GitHub organization for repositories with the
- Block known network indicators:
- Block
scan.aquasecurtiy[.]orgat the network perimeter (note the typosquat: extrarin “security”) - Resolves to:
45.148.10.212 - Note: ICP canister C2 (
tdtqy-oyaaa-aaaae-af2dq-cai) cannot be blocked via traditional DNS filtering
- Block
Long-term Recommendations
- CI/CD supply chain hardening:
- Pin all third-party GitHub Actions to commit SHAs rather than mutable tags
- Implement least-privilege scoping for CI/CD runner secrets – separate credentials per pipeline where feasible
- Establish a credential rotation policy that is validated to completion, not just initiated, following any CI/CD security incident
- Monitor for unexpected outbound network connections from pipeline runners as a standing detection
- Dependency and package governance:
- Maintain an inventory of npm and PyPI packages used in CI/CD and agentic tool environments
- Subscribe to security feeds for packages in your dependency tree
- Evaluate use of dependency pinning and integrity verification (e.g., lockfiles, hash verification) for packages executed in automated pipelines
- Treat packages executed in the March 19 – 24 window as suspect until individually verified
- Agentic AI environment security:
- Audit dependency trees of packages loaded dynamically in agentic tool environments
- Apply the same credential rotation scope to agentic systems as to traditional CI/CD runners – agents operating with cloud or Kubernetes access are exposed to the same credential compromise as any other pipeline runner
- Review tool invocation paths in agentic pipelines that call terminal environments or package managers, as these represent direct exposure points for supply chain attacks of this type
Framework Context
This incident aligns with multiple security frameworks:
- Geordie Supply Chain: Compromise of a trusted third-party tool used in agentic and CI/CD pipelines illustrates supply chain risk at the tooling layer.
- Geordie Credential Exposure: Secrets harvested from pipeline runner memory during execution, including cloud provider tokens, GitHub PATs, and Kubernetes credentials.
- Geordie Code Execution: Malicious code injected into trusted binaries and GitHub Actions executed with pipeline-level trust across thousands of CI/CD environments.
- Geordie Configuration: Incomplete credential rotation following initial detection (March 1) left residual access that enabled the primary attack.
- OWASP ASI ASI04:2026 Agentic Supply Chain Vulnerabilities: Agentic ecosystems that compose capabilities at runtime from third-party tools inherit the same exposure demonstrated by this campaign’s compromise of Trivy, LiteLLM, and npm packages.
- OWASP AIVSS AIVSS-CR8: Agent Supply Chain and Dependency Risk: Compromised libraries and tools introduced into the agentic execution chain through supply chain attacks affecting agent behavior at runtime.
- OWASP AIVSS AIVSS-CR3: Agent Cascading Failures: Credentials stolen from one project enabled compromise of at least two additional downstream projects within five days, demonstrating cross-system exploitation and cascading damage.
- OWASP AATM T3 Privilege Compromise: Credential reuse across pipelines enabled lateral movement from Trivy into Checkmarx and LiteLLM using harvested tokens.
- OWASP LLM LLM03:2025 Supply Chain: Backdoored versions of Trivy and LiteLLM were distributed through official package registries, compromising the integrity of the software supply chain.
Updates
We will update this analysis as more information becomes available. Please monitor our security channels for the latest updates.
References: Aqua Security • Wiz • Sysdig • Aikido – Kubernetes wiper • Mend – CanisterWorm • Socket – npm packages • JFrog – CanisterWorm • Endor Labs • BleepingComputer • Microsoft Security Blog • KrebsOnSecurity • GitGuardian • ramimac.me
More Articles


.svg)
.png)

